Major IT outage affecting banks, airlines, media outlets across the world
Major IT outage affecting banks, airlines, media outlets across the world

www.abc.net.au
Live: Major IT outage affecting banks, airlines, media outlets across the world
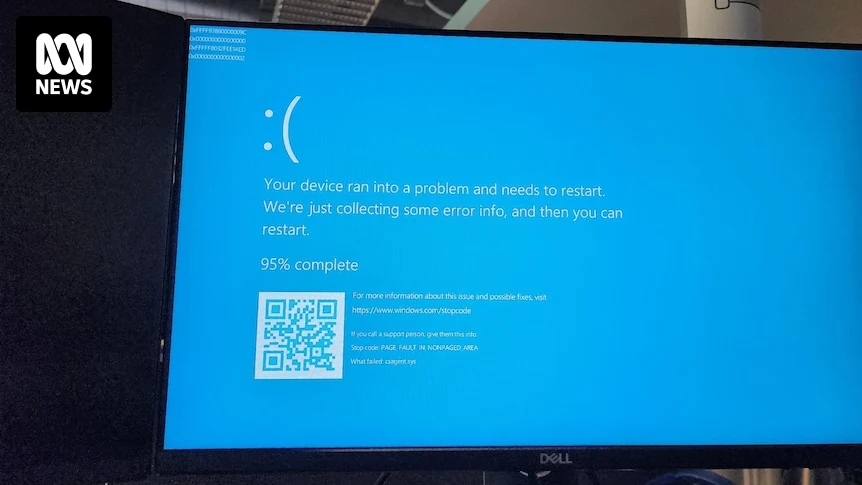
All our servers and company laptops went down at pretty much the same time. Laptops have been bootlooping to blue screen of death. It's all very exciting, personally, as someone not responsible for fixing it.
Apparently caused by a bad CrowdStrike update.
Edit: now being told we (who almost all generally work from home) need to come into the office Monday as they can only apply the fix in-person. We'll see if that changes over the weekend...
