I didn't know you were supposed to disable root user...
I didn't know you were supposed to disable root user...


Background: 15 years of experience in software and apparently spoiled because it was already set up correctly.
Been practicing doing my own servers, published a test site and 24 hours later, root was compromised.
Rolled back to the backup before I made it public and now I have a security checklist.
You're viewing a single thread.
Lol you can actually demo a github compromise in real time to an audience.
Make a repo with an API key, publish it, and literally just watch as it takes only a few minutes before a script logs in.
46 0 ReplyI search commits for "removed env file" to hopefully catch people who don't know how git works.
30 0 Reply--verbose please?
edit: never mind, found it. So there's dumbasses storing sensitive data (keys!) inside their git folder and unable to configure .gitignore...
13 0 Reply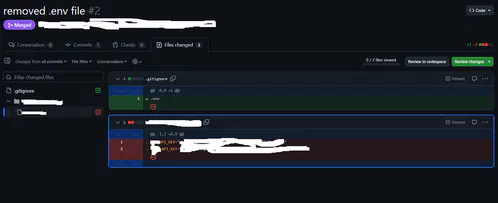 yeah, I just tried it there, people actually did it.
yeah, I just tried it there, people actually did it.12 0 ReplyMy work is transferring to github from svn currently
4 0 ReplyMy condolences
4 0 Reply
You gremlin lmao
10 0 Reply