Point it out explicitly in your resume. Don't expect them to figure out your github activity on their own.
It's definitely better to have open source experience than no experience.
Anyone aware of a way to run gF programmatically (i.e. lua) but with a different value instead of what's under the curser?
How many programmers does it take to filter out 36 characters? You may think this is an opening to a joke, but it’s not.
It takes a special kind of person to name a company after their own body part. Fortunately the Microsoft Security Response Center doesn’t seem to have inherited that kind of mentality, because when I have reported not a bug but a feature as a vulnerability - they accepted it.

cross-posted from: https://infosec.pub/post/5707149
> I talk about a report I've made to MSRC in the beginning of the year regarding vscode. > > It's a bit different. There's no in depth technical stuff, because I basically just reported the feature, not a bug.
For Linux there's gnome keyring.
I think technically what they sell is services related to RHEL and not it itself (correct me if I'm wrong).
To me at least, a big problem with it is the hypocrisy. RHEL started itself by repackaging another piece of software. Why is it not OK for others to do the same to them? Especially when the gpl license allows that, and requires them to allow that!
The Linux license allows anyone to distribute it for profit (under certain conditions). If I wanted to sell CDs with the Linux kernel I could. Wouldn't be a good business, but I could.
Would've never expected this read to be so interesting.
Twitter's rate limit changes have led to the death of third-party apps like Apollo
Apollo?
Twitter implemented a rate limit to manage their infrastructure migration to Raspberry Pi
Raspberry pi?
Elon Musk is supposedly fighting against the CIA and NSA, who are using Twitter for censorship
Wha...?
I doubt they run on windows tbh. If they take issue with with monolithic design of Linux, then windows would be an even bigger problem.
Also, most of the devices in question are probably small controllers, incapable of running windows. (Microsoft are struggling to run it on arm so...)
Yeah, didn't get that one either.
That makes sense, and yeah I imagine the problem isn't the entertainment system.
I just don't get the the last paragraph. I don't know if using Linux affects their code being OS or not. If they're just running it on top of Linux and not modifying it, it probably won't be a GPL violation to keep it closed.
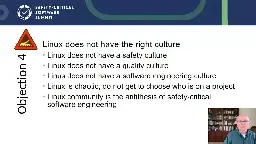
ELISA (Enabling Linux in Safety Applications) Project announced that Boeing has joined as a Premier member, marking its commitment to Linux and its effective use in safety critical applications. Hosted by the Linux Foundation, ELISA is an open source initiative that aims to create a shared set of tools and processes to help companies build and certify Linux-based safety-critical applications and systems
I imagine this means they're contributing both actively and financially to Linux.
Regarding section 1, won't you still get the conflicts when pushing to remote (or pulling from it)?
Some thinkpads have official support for Ubuntu by the manufacturer (lenovo), which means battery optimizations out of the box, amongst other things. Might be relevant for your laptop.
cross-posted from: https://programming.dev/post/368257
> Thoughts?
cross-posted from: https://programming.dev/post/276519
> Is anyone aware of the state of modern standby (S0ix/S2idle) in ubuntu? > > From what I can gather, there is support for it in the kernel, but I couldn't find any specifics regarding ubuntu (there is a post on reddit but the subreddit is set to private...).
I now noticed that the post's content differs between instances, sorry about that.
I could be wrong. I'd be happy to be shown wrong. Always room to learn.
Generally when I hear cyber security I think of things like data breaches, vulnerability research, malware analysis, netsec, appsec... Stuff like that.
I'm actually not really sure where I'd have posted. I remember seeing a meta community somewhere, maybe lemmy.world, where you can have discussions about Lemmy. But I'm really not sure.
And just to make it clear, I'm just giving you my honest opinion. Not trying to make you feel bad or anything.
How is is this cyber security related?
And it's not P2P...
Jami is p2p for example. Direct communication between peers.
Any recommendations for a trust worthy and reliable domain registrar?
A (reasonably) condensed version of two weeks' worth of heated GPL argument.

That's not being pretentious, that's being blunt. I personally as a dev, appreciate that.
If you think the code can be improved you should say that, and exactly why that's the case. When you're mistaken you should be able to take the criticism.
Your mission as a dev is to write the ideal code, and being overly polite can stand in the way of that.
He was probably working with bytes and not individual bits, but yeah. He basically wrote executables directly (to my understanding).
I don't think he does. If you're talking about the third line, there's a space between the dots.
The dot command is equivalent to source (running the script in the context of the current shell).
Is anyone aware of the state of modern standby (S0ix/S2idle) in ubuntu?
From what I can gather, there is support for it in the kernel, but I couldn't find any specifics regarding ubuntu (there is a post on reddit but the subreddit is set to private...).